Safiya Dodojonova
Cybersecurity: Protecting Our Digital World
In today’s digital age, individuals increasingly rely on online systems, social media platforms, and mobile applications for communication, education, and financial transactions. While these technologies offer convenience and connectivity, they also expose users to a growing number of cyber threats, including phishing attacks, malware, and data breaches. Cybersecurity, the discipline dedicated to protecting digital systems, networks, and information, plays a critical role in maintaining the confidentiality, integrity, and availability of data—commonly known as the CIA triad (IBM, n.d.). This principle represents the gold standard for information security: Confidentiality ensures data is accessible only to authorized users, Integrity ensures information has not been tampered with, and Availability ensures systems remain operational when needed.
In Tajikistan, as internet adoption and mobile banking services expand, both individuals and institutions face increasing risks from cybercrime (OSCE Programme Office in Dushanbe, 2025). Students, in particular, are vulnerable to scholarship scams and social media fraud. Recent data from 2025 indicates that 85% of mobile phishing attacks now occur outside of email—through messaging apps and social networks—specifically targeting younger demographics who rely on mobile devices for education (SentinelOne, 2026). Understanding these threats is crucial not only for protecting personal data but also for fostering a safer digital environment for the wider community.
This article examines: How can educational institutions and individuals in Tajikistan protect themselves against evolving cyber threats within the constraints of limited resources and awareness? The following sections explore the current cybersecurity landscape in Tajikistan, highlight emerging global trends such as AI-driven attacks and ransomware-as-a-service, examine national and regional initiatives, discuss the specific risks faced by students, and provide strategies for mitigating cyber threats effectively.
Importance of Cybersecurity
In Tajikistan, increasing internet penetration and growing reliance on digital platforms have made cybersecurity awareness particularly important. Students and young users frequently depend on online services for academic communication, financial transactions, and social networking. The education sector worldwide has become a significant target for cybercriminals due to large volumes of sensitive data and often limited security infrastructure (Chin, 2025). This high level of digital engagement, combined with limited security awareness, can increase exposure to cyber risks. Cybercriminals often exploit this vulnerability through fraudulent online offers, phishing emails, and manipulated social media content. By January 2025, Tajikistan had approximately 6.07 million internet users, representing a penetration rate of 56.8% — growing by 113,000 new users in a single year (DataReportal, 2025). Despite this expansion, mobile internet infrastructure remains underdeveloped, with Tajikistan ranking 139th out of 143 countries in mobile internet speed (DataReportal, 2025). This combination of rapid digital growth and weak infrastructure creates a widening cybersecurity exposure gap that institutions are currently ill-equipped to close.
Beyond individual consequences, cybersecurity has broader economic and national implications. Disruptions to digital infrastructure can affect banking systems, public services, and communication networks. Therefore, investing in cybersecurity education, preventive technologies, and responsible digital behavior is critical not only for personal protection but also for national digital stability.
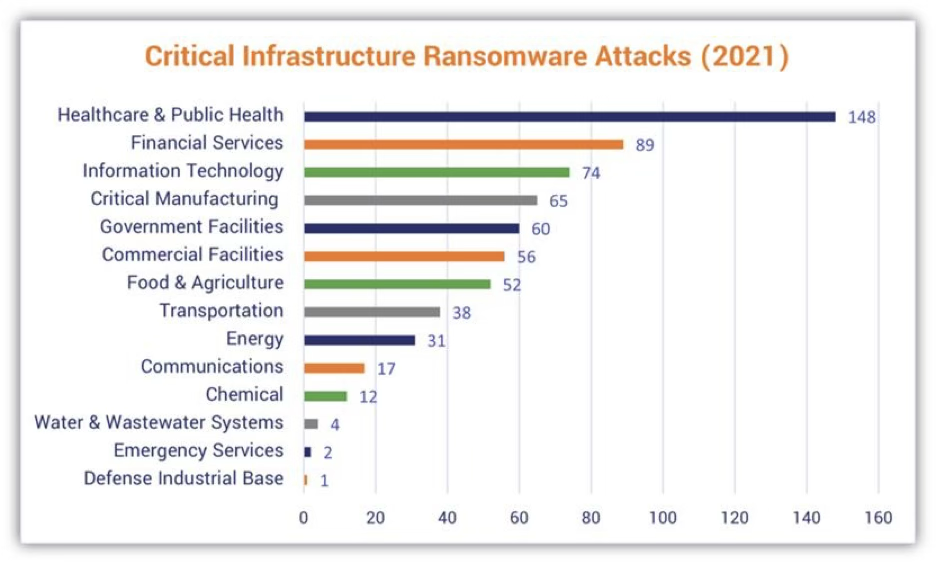
Figure 1. Ransomware attacks on critical infrastructure sectors in the United States (2021).
Source: Cybersecurity and Infrastructure Security Agency (CISA). (2021). Critical infrastructure ransomware attacks data. U.S. Department of Homeland Security.
Types of Cyber Threats
Cyber threats continue to evolve in response to technological advancements and increased digital connectivity. Rather than targeting only technical vulnerabilities, many modern attacks exploit human behavior, weak security practices, and insufficient awareness. Global cybersecurity reports indicate that threat actors are increasingly combining technical tools with social engineering techniques to maximize impact (IBM, n.d.). Understanding the different forms of cyber threats is essential for individuals, students, and institutions seeking to reduce digital risk.
One of the most widespread threats is malware, a general term describing malicious software designed to infiltrate or damage digital systems. Malware can take many forms, including spyware, Trojans, and keyloggers. These programs often enter systems through unsafe downloads, compromised websites, or deceptive email attachments. Once installed, malware may steal personal data, monitor user activity, or disrupt system operations (SentinelOne, 2026).
Another common threat is phishing, a form of social engineering that manipulates users into voluntarily providing sensitive information. Phishing attacks typically appear as legitimate emails, messages, or websites that imitate trusted organizations. In educational contexts, attackers may disguise phishing attempts as scholarship notifications, university announcements, or job opportunities. Because phishing relies on human trust rather than technical weakness, awareness and critical thinking are key defenses (IBM, n.d.). Globally, phishing emails increased 17.3% between September 2024 and February 2025 compared to the preceding six-month period, and phishing is projected to be a factor in 42% of all global breaches (WEF, 2026).
Ransomware represents a more aggressive type of malware. It encrypts files or locks users out of their systems, demanding payment in exchange for restored access. Such attacks can have severe consequences for educational institutions and businesses, potentially halting operations and causing financial losses. Reports on cybersecurity in the education sector highlight the growing frequency of ransomware incidents targeting schools and universities (Chin, 2025) This trend emphasizes the importance of regular data backups and system monitoring.
In addition to these threats, attacks such as Denial of Service (DoS), Man-in-the-Middle (MitM) attacks, and SQL injection target network infrastructure and web applications. These methods exploit system vulnerabilities to interrupt services, intercept communications, or gain unauthorized access to databases. Unlike phishing, which focuses on deception, these attacks rely more heavily on technical system weaknesses (SentinelOne, 2026).
Together, these cyber threats demonstrate that cybersecurity is not solely a technical issue but also a behavioral and organizational challenge. Effective protection requires a combination of secure technologies, informed users, and proactive risk management strategies.
Cybersecurity in Education: The Tajikistan Perspective
The digital transformation of education has significantly expanded the exposure of schools and universities to cyber risks. In Tajikistan, the growing integration of online learning platforms, electronic administration systems, and digital financial services has created new vulnerabilities within the educational sector (OneEducation, 2025). As internet usage and mobile connectivity increase nationwide, educational institutions must confront cybersecurity challenges that were previously limited to corporate environments. The scale of this challenge is striking: in 2025, educational institutions globally averaged 4,388 cyberattacks per organization per week — more than double the cross-sector average (Check Point Research, 2025). Globally, 91% of higher education institutions reported experiencing a breach or cyberattack in the preceding 12 months, with 30% facing attacks at least weekly (BitLyft, 2026).
Why Educational Institutions Are Attractive Targets
Schools and universities maintain extensive databases containing personal, academic, and financial information (BitLyft, 2026). These datasets often include student identities, contact information, grades, tuition records, and research materials. Because such information holds monetary and strategic value, it becomes highly appealing to cybercriminals.
Institutions operating with outdated infrastructure or decentralized networks face even greater risks. Attackers frequently exploit weak system configurations, unpatched software, and insufficient monitoring mechanisms (OneEducation, 2025). In addition to financial motives, universities conducting research may also attract actors seeking intellectual property or sensitive data. The financial consequences are severe: in 2025, the average cost of a data breach in the education sector reached $3.80 million per incident, while ransomware attacks alone exposed 3.9 million student records globally — a 27% increase over the prior year (IBM, 2025; Verizon, 2025).
Human manipulation remains one of the most effective attack methods. Students and academic staff may unintentionally disclose login credentials or download malicious attachments disguised as official communications. Reports from cybersecurity awareness initiatives in Tajikistan indicate that phishing represents a growing concern within the educational sector (OSCE Programme Office in Dushanbe, 2025). Since these attacks rely on deception rather than technical exploitation, limited awareness significantly increases vulnerability.
Ransomware incidents can disrupt institutional operations at multiple levels. When academic databases are encrypted, enrollment systems, grading platforms, and administrative records become inaccessible. Beyond operational paralysis, financial recovery costs can be substantial. In 2025, the average recovery expense for educational institutions globally exceeded several million dollars (Canadian Centre for Cyber Security, 2026). For resource-constrained systems, such costs can have long-term consequences.
DDoS attacks overwhelm institutional servers by flooding them with traffic, making online platforms unavailable. In academic contexts, such disruptions are particularly damaging during examination periods or admissions deadlines (Chin, 2025). Even short interruptions can affect academic performance and institutional credibility.
Factors Increasing Vulnerability
Several structural and behavioral factors amplify cybersecurity risks in Tajikistan’s educational system.
The expansion of remote learning since 2020 has multiplied the number of personal devices connected to institutional systems (BitLyft, 2026). Each personal laptop or smartphone effectively becomes a potential entry point for attackers if not properly secured.
Additional contributing factors include:
- Budget limitations, which restrict investment in modern cybersecurity infrastructure (OneEducation, 2025).
- Limited cybersecurity awareness among students and educators, increasing susceptibility to phishing and social engineering (OSCE Programme Office in Dushanbe, 2025).
- Legacy software systems, which often lack vendor support and remain vulnerable to known exploits (BitLyft, 2026).
These challenges demonstrate that cybersecurity in education is not purely a technical issue but also a matter of institutional capacity and policy prioritization.
These structural vulnerabilities translate directly into real harm. Cyber incidents can produce both immediate and long-term consequences. Operational disruptions may interrupt teaching schedules and administrative processes. Personal data breaches undermine trust among students and parents, while financial losses from system restoration or ransom payments can strain already limited budgets (OneEducation, 2025).
Furthermore, reputational damage may influence enrollment rates and public confidence in institutional management.
Strategic Mitigation Measures
Addressing these risks requires a layered and realistic strategy. Experts emphasize combining technical safeguards with user education (OSCE Programme Office in Dushanbe, 2025; BitLyft, 2026).
Recommended measures include:
- Maintaining updated software and applying security patches regularly
- Implementing structured cybersecurity awareness training programs
- Establishing clear incident response protocols
- Conducting security assessments of third-party vendors
- Applying two-factor authentication for critical systems
While advanced measures such as AI-based monitoring tools and Virtual Private Networks (VPNs) provide additional protection, their implementation demands financial and technical resources that may not be readily available in all Tajik institutions.
For resource-limited schools, prioritizing high-impact and cost-effective actions—such as mandatory phishing awareness training and enforcing multi-factor authentication—may offer the most practical starting point. Gradual improvement based on risk assessment allows institutions to strengthen digital resilience without exceeding budgetary constraints.
Cybersecurity Trends
Artificial Intelligence in Cybersecurity
Artificial intelligence has transformed cybersecurity into a dynamic and automated battlefield (IBM, n.d.). Defensive systems now rely on machine learning to detect irregular login behaviors, suspicious network traffic, and automated bot activity. For example, educational institutions may use AI-driven monitoring tools to flag unusual student access patterns that suggest compromised credentials.
At the same time, attackers are also leveraging AI technologies. Autonomous attack systems can continuously probe institutional websites and digital platforms for vulnerabilities without constant human direction. This creates an imbalance: cybercriminals can operate at scale with automation, while institutions—particularly those with limited technical resources—struggle to respond efficiently. For Tajik educational institutions, the challenge lies in adopting AI tools while ensuring sufficient expertise to manage them effectively. The data reflects this shift: by early 2025, AI-powered methods accounted for more than 80% of social engineering activity, and 87% of organizations reported that AI-generated techniques such as deepfakes were making phishing attempts significantly harder to detect (WEF, 2026). AI-generated phishing lures have been shown to increase click-through rates by up to 54% compared to conventional methods (SentinelOne, 2026).
Zero Trust Security Models
Traditional cybersecurity approaches often assumed that users inside a network could be trusted. The Zero Trust model challenges this assumption by requiring continuous verification of users, devices, and behavior (SentinelOne, 2026). Access is not permanently granted; instead, it is repeatedly validated.
In a university setting, this means that even if a student logs into the campus network, additional checks may be performed before granting access to academic records or financial systems. Although Zero Trust significantly reduces internal breach risks, implementation demands financial investment and technical specialization. In resource-limited environments, partial adoption—such as applying Zero Trust only to sensitive systems—may provide a realistic compromise.
Ransomware-as-a-Service (RaaS)
Ransomware has evolved from isolated criminal activity into a structured commercial model (Canadian Centre for Cyber Security, 2026). Cybercriminal groups now develop ransomware tools and lease them to affiliates who conduct attacks in exchange for a profit share. This subscription-style structure lowers the barrier to entry for cybercrime. Between Q1 2024 and Q1 2025, ransomware attacks tripled globally — rising from 572 to 1,537 recorded incidents — and annual damage costs from ransomware are forecast to reach $74 billion by 2026 (Canadian Centre for Cyber Security, 2026).
As a result, even smaller educational institutions can become targets. Attackers no longer require advanced coding skills; access to ready-made ransomware kits is sufficient. This development increases risk exposure for schools and universities with limited cybersecurity budgets.
The Evolution of Multi-Factor Authentication
While multi-factor authentication (MFA) has become standard practice, traditional SMS-based codes are increasingly vulnerable to interception methods such as SIM-swapping (SentinelOne, 2026). Newer systems rely on adaptive authentication mechanisms that assess contextual risk factors.
For instance, access from a familiar device in a usual location may require minimal verification, whereas login attempts from unfamiliar regions may trigger biometric or hardware-based authentication. This risk-based approach enhances security while maintaining usability for legitimate users.
Human-Centered Security Training
Traditional awareness campaigns that provide generic warnings have demonstrated limited effectiveness (BitLyft, 2026). Modern approaches emphasize behavioral analysis and personalized training simulations.
Instead of applying identical training to all users, institutions analyze patterns of susceptibility and tailor simulations accordingly. Gamified exercises and scenario-based learning encourage deeper engagement, transforming cybersecurity from a compliance obligation into an active learning process.
Awareness of cybersecurity developments enables institutions to adopt preventive strategies rather than reactive responses. By identifying emerging risks early, schools can allocate limited financial and technical resources more effectively. For countries such as Tajikistan, where cybersecurity infrastructure is still developing, strategic planning and informed policy decisions can significantly strengthen digital resilience (OSCE Programme Office in Dushanbe, 2026).
Ultimately, understanding trends is not merely about technology—it is about preparedness, sustainability, and long-term digital stability.
Conclusion
In Tajikistan, where cybersecurity infrastructure is still developing and resources are constrained, effective protection cannot rely on enterprise-grade solutions alone. The evidence reviewed in this article points to three high-priority, cost-effective actions: mandatory phishing awareness training, enforcement of multi-factor authentication on critical systems, and regular software patching. These measures address the most common attack vectors—social engineering, credential theft, and unpatched vulnerabilities—without requiring advanced technical infrastructure or large budgets. For institutions such as DII and Tajikistan’s broader higher education sector, these practical steps represent the most direct path toward improved digital resilience (OSCE Programme Office in Dushanbe, 2025; BitLyft, 2026).
Cybersecurity is not a problem that can be solved once and forgotten. As AI-driven attacks and ransomware-as-a-service models lower the barrier for cybercriminals, threats will continue to evolve faster than institutional defenses. The sustainable response for resource-limited environments is not to match attackers in technical sophistication, but to build a culture of security awareness—where every student, educator, and administrator understands that their behavior is the first and most important line of defense. Achieving this in Tajikistan requires cooperation between universities, government bodies, and international partners such as the OSCE, transforming cybersecurity from a technical obligation into a shared national priority.
References:
Barrinha, A., & Turner, R. (2024). Strategic narratives and the multilateral governance of cyberspace: The cases of European Union, Russia, and India. Contemporary Security Policy, 45(1), 72–109. https://doi.org/10.1080/13523260.2023.2266906
BitLyft. (2026). The state of higher education cybersecurity: insights and trends. https://www.bitlyft.com/resources/the-state-of-higher-education-cybersecurity-insights-trends
Canadian Centre for Cyber Security. (2026). Ransomware threat outlook 2025–2027. Government of Canada. https://www.cyber.gc.ca/en/guidance/ransomware-threat-outlook-2025-2027
Caspian Post. (2025). Tajikistan‑Kyrgyzstan deepen ties on cybersecurity and border cooperation. https://caspianpost.com/tajikistan/tajikistan-kyrgyzstan-deepen-ties-on-cybersecurity-and-border-cooperation
Check Point Research. (2025). Cyber attack trends: Mid-year report 2025. https://www.checkpoint.com/press/2025/check-point-research-reports-a-100-increase-in-cyber-attacks/
Chin, K. (2025, January 8). Education sector cyberattacks: Trends and risks. UpGuard https://www.upguard.com/blog/education-sector-cyber-attacks
DataReportal. (2025). Digital 2025: Tajikistan. https://datareportal.com/reports/digital-2025-tajikistan
IBM. (2025). Cost of a data breach report 2025. https://www.ibm.com/reports/data-breach
IBM. (n.d.). Cybersecurity trends: IBM’s predictions for 2025. https://www.ibm.com/think/insights/cybersecurity-trends-ibm-predictions-2025
OneEducation. (2025). Why cyber‑attacks in schools are surging in 2025. https://www.oneeducation.co.uk/why-schools-are-now-prime-targets-for-cyber-attacks-in-2025/ OSCE Programme Office in Dushanbe. (2025). Cybersecurity initiatives. https://dushanbe.osce.org/programme-office-in-dushanbe/599861
SentinelOne. (2026). 10 cyber security trends for 2026. https://www.sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-trends/
Verizon. (2025). 2025 data breach investigations report. https://www.verizon.com/business/resources/reports/dbir/
World Economic Forum. (2026). Global cybersecurity outlook 2026. https://reports.weforum.org/docs/WEF_Global_Cybersecurity_Outlook_2026.pdf



